Hackers stay up at night to get better at their job, which is breaking device security on your latest electronic design. Electrical engineers and computer scientists need a similar work-ethic to harden their assemblies against bad-actors. Over the next two posts we will cover embedded security to help educate our customers about privacy, security, and encryption and offer tips on how to improve the design of your next printed circuit board.
The chorus of the old Petula Clark song says “There’s never been a horse that couldn’t be rode. Never was a cowboy that couldn’t be throwed…” Electrical engineers will forever be in the business of making devices hackerproof, only to find out later that the devices can be hacked. But that doesn’t mean that you should throw up your hands in despair. Some simple design tips, tricks, and techniques can help you encourage your adversary to move on to somebody else’s electronic design. Eventually your prototype will enter production and go into the field. Hopefully your circuit design is of no interest to bad actors, and will survive its service life without being hacked. But, as the chorus of the same song reminds us “…You pays yer money and you takes yer chances.”(1)
About Your Adversary
Black-Hat hackers are electrical engineers and computer scientists whose moral compass does not necessary point in the right direction. Usually, they are people who love a challenge. Hackers tend to look for problems to solve, and then they go out and solve them. Financial compensation motivates some, but for most the real reward is the emotional satisfaction of solving a problem or beating their adversary. Sounds a lot like an engineer, right? Too bad they’re working against you instead of with you.
The good news is that most of the people who think of themselves as “hackers” are not hackers at all, at best they are script-kiddies. Script-kiddie is the pejorative phrase for people who take the work of hackers and replicate it. It’s similar to the difference between a gifted oil-painter and the guy running the color copy machine at the local office store. Script-kiddies can press buttons, but usually have limited or no ability to generate novel attacks of their own, nor are they able to generalize the work of other attacks and apply them to new scenarios, and they typically cannot overcome problems when they arise. You can make your design kiddie-proof relatively easily.
The goal of most engineers should be to stop all script-kiddies and almost all hackers. In reality though, if a state-sponsored hacker group wants to steal the secrets from your designs, there is nothing most engineering teams can do to stop them — because if they fail to get the secrets hidden in the silicone, security services have plenty of experience compromising the individuals involved in its design. You can however, make things very, very difficult for your adversary, and hope they lose interest, or lack the technical wherewithal to beat you.
Getting Started
In a recent interview (3), Joe Grand, an ethical-hacker, shared with us how hackers target printed circuit boards. He starts by gathering publicly available information, and then looks for programming points, data buses, etc…, followed by more advanced attacks, such as simple power analysis and differential power analysis, chip decapping, etc…. It usually doesn’t take long for him to find an entry point.
So how do you even begin to deal with these problems?
Remove Information
This is sometimes referred to as “security through obscurity.” If you use this as your only means of hardware security, your design deserves to be hacked. At best, it provides a minor speed bump to an adversary. This design philosophy deters hackers in the same way “Security Camera” signs deter thieves.
As an engineer, what the marketing and sales teams do is likely beyond your control. But there’s a good chance the marketing team doesn’t care which microprocessor and sensor you chose anyway, they just want to know what the device does, so keep details sparse if possible.
Engineers get to design the circuit board, so focus on removing information there. Some assembly shops will allow you to populate a board with a silk-screen layer that doesn’t include product reference designators — only pin 1 designators. At the same time, some integrated circuit manufacturers will provide you with a custom run of integrated circuits with no top-side markings other than batch number, date code, and pin 1 designator.
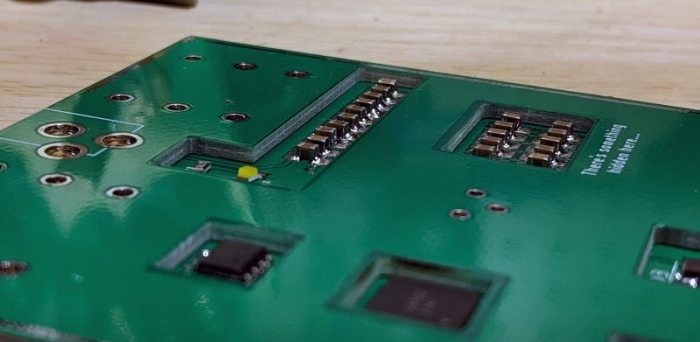
This edited partial image of a PCB from a major manufacturer’s sensor solution gives no hint as to what the parts are nor what they do. This was provided to me several years ago as a marketing sample so that I might investigate and write about the device performance without disclosing specific information before the company was ready. Their efforts at obscurity were thwarted by an employee that included a series of hand-written sticky-notes with part numbers in the shipment.
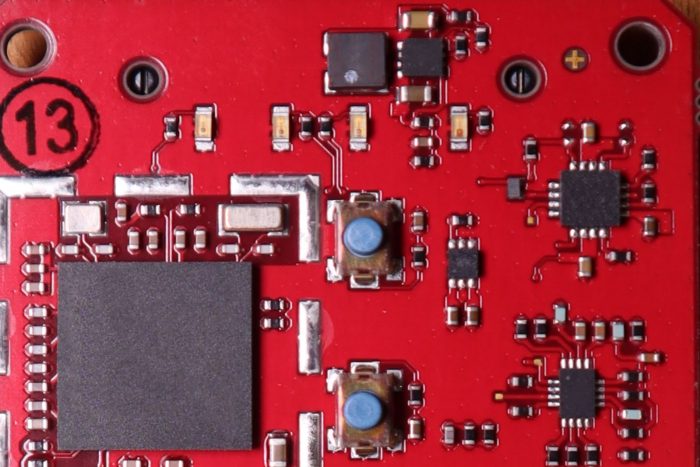
There are so many parts out there that share a common footprint that most people would be forced to stop there. But at the very least, you’ve now caused the hacker to find an x-ray machine or high-powered microscope and bottle of acid to even begin to determine which-type of IC is encased in which epoxy shell. Once they have that knowledge, they still have to determine the part type, the manufacturer, and product line. With all of the products currently on the market with a similar footprint, that will usually take a decent amount of time. These actions will not stop a state-sponsored, or even a dedicated independent hacker, but a script-kiddie should be sufficiently frustrated at this point that they choose to move on to someone else’s product.
It’s worth repeating that if “security through obscurity” is your only security measure, you are only frustrating yourself and your PCB assembly company. Your electronic design will absolutely be hacked. This philosophy, at best, slow down an adversary by a few hours. But it will keep the kiddies at bay.
Next, we will investigate some security ideas that are more advanced than simply omitting the silk-screen layer.
More Sophisticated Speedbumps
The following options are only suggestions for a production run, and only if you have something that is of high value to a hacker. For a prototype or small batch pcb run, implementing many of the following suggestions will only serve to frustrate the design engineer, the PCB manufacturing company, and the PCB assembly companies (or Turnkey) that you work with. So put on your tin-foil hat and join me as we go down the rabbit-hole.
Remove Access to Pads, Vias, and Traces
Choose Parts with No Leads
Begin by choosing BGA and other leadless footprints for your ICs. These parts connect to printed circuit boards without providing a potential probe point. Electrical connections are taken from the BGA parts down to intermediate layers of the board where they will stay until they re-emerge under a sensor. With no probe points to touch, an adversary cannot intercept inter-chip communications or reprogram/debug the IC.
Bury Your Traces
Place the parts on the outer layers of your board, and ensure the outer layers are ground-planes with plenty of through-hole via stitching to internal ground layers so you reduce the opportunity for unintended emissions.
Remove Programming Headers
Without those pads / test points, how will you program your ICs and test your boards? Many ICs can be factory programmed, which solves one problem. But there are other, more creative solutions.
For example, on the prototype, you might bring test-points to the surface via blind vias. On production runs, simply make the blind vias buried vias and remove the corresponding pads from the outer layers of the design. Replacing the area on the outer layer with a copper pour helps reduce the opportunity for the detection of radiated emissions from your transmission lines.
Break-Away Headers
Use a series of mouse-bites to create a weakness in a small protrusion on your PCB that houses a programming header. After the design is confirmed to be working, break off the header — the net access will disappear into the side of the board. If the layer that carries the programming traces is 0.25 oz/ft² copper, you can use trace/space widths as small as 3 mil / 3 mil to carry the signals to the breakaway part of the board. That would make it very, very difficult to find those conductors again with a probe. The tight vertical spacing of layers would make it difficult to probe without short-circuiting one probe point to the next. After you remove the header, it’s safe to assume any firmware updates to your design will have to be Over-The-Air updates (OTA).
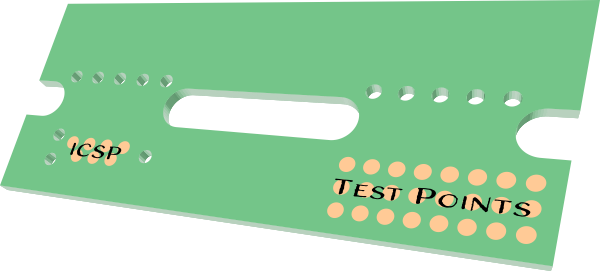
This drawing shows Testpoints and an In-Circuit-Serial-Programming connection moved off of the main circuit board. Electrical Connections between the testpoints, the ICSP, and the mainboard would be made on multiple inner layers that would no longer be accessible after separation. The signal integrity of this design is poor, so the clock rate of the programmer should be reduced as needed to successfully program the microcontroller.
One-Time Solder Paste
So what is to keep an adversary from simply removing your ICs from your board and making a new one that has convenient breakout points on it? The answer is Transient Liquid Phase Sintering (TLPS) paste. This is a type of solder-paste meant for high-operating temperature and high-reliability printed circuit boards. It is made of a mixture of metals including tin and copper. When the tin initially melts, it bonds with the copper, and creates a series of intermetallic bonds that eliminate the liquid phase of the new material. Without the liquid phase, the bonds between the IC and your board are solid and permanent. No rework is possible without first destroying the integrated circuit, so you will certainly want to get your thermal profiles dialed in before a production run.
I first learned of this technology from Chris Hunrath (4), the VP of technology at Insulectro.
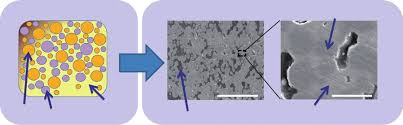
This image, taken from a technical paper by HitachiChemical (5) shows the mixture of metals forms a new compound after-heating. After combination, the intermetallic bonds cause the melting temperature to increase significantly.
Take the concept of embedded to a whole new level
It is now possible to embed your ICs inside of your printed circuit boards as part of the layer stackup. Not every manufacturer is comfortable with the techniques involved, and the price is high, but it is possible. Hacking embedded devices would certainly require destructive methods, further frustrating an adversary.
This image from Hackaday.com shows integrated circuits and passive components embedded in a PCB stack. Some manufacturers are able to place the ICs in intermediate layers of their design. (6)
This technology can also be used for nefarious purposes. To see how Chinese Hackers appear to have compromised an entire supply-chain with embedded chips, see The Big Hack (7) article in Bloomberg business.
Use Embedded Planar Capacitance
When digital logic changes inside an integrated circuit, it disturbs the power rails that feed a chip. Clever hackers have developed a technique known as Differential-Power-Analysis that uses the varying power-line consumption caused by gate switching to determine the state of logic inside the chip. This is used to determine instructions, read memory, etc… The first line of defense against this attack is to use a microprocessor specifically engineered to defend against it. But you can help the microprocessor out by smoothing out the power consumption near the IC.
Electrical Engineers often use surface-mount capacitors on their printed circuit boards to decouple integrated circuits from the rest of the circuit board. Hackers will often remove the capacitor, or replace it with a 50-ohm resistor, and initiate the attack. One way to mitigate the noise generated by gate switching is to embed decoupling capacitors into your circuit board stackup. After all, a capacitor is nothing more than two conductors separated by a dielectric — so make your capacitors from two adjacent layers of your PCB stackup separated by a very thin laminate material.
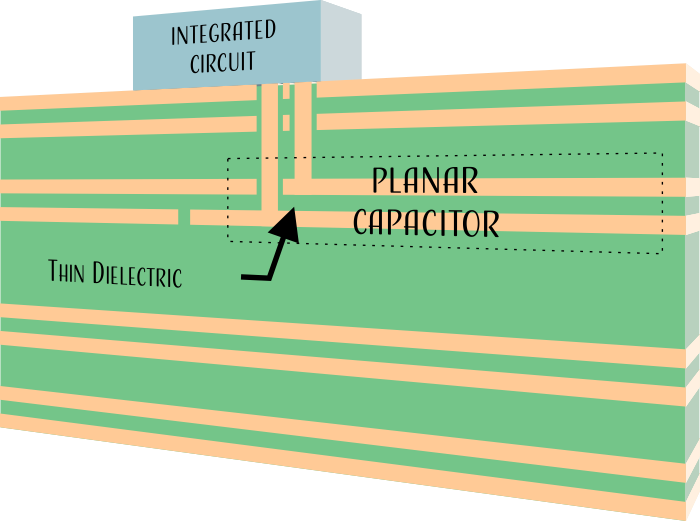
Embedded Capacitors and Planar Capacitors can save valuable circuit board space as well as reduce the effects of ground bounce.
By decoupling the integrated circuit inside the board stack, preferably directly below the IC to minimize inductive loops, you are reducing the amount of ground-bounce and Vcc-Dip that occurs with each switching logic-gate. This does not remove all the noise from your design — but every little bit helps. The idea is to reduce the signal-to-noise ratio of the power-rail perturbations so that one state-dependent power-signature looks a lot like another state-dependent power-signature. This frustrates the hacker and increases the capture time required for Differential-Power Analysis. If you cause your adversary to spend a day/week capturing signals from your device to collect enough data to decrypt a key, but you use Elliptic-Curve Ephemeral Diffie-Hellman to create a new shared secret for each data transaction, you will stay well ahead of your attacker. To learn about buried capacitors, see “The Buried Capacitance Design Guide” by HADCO (8).
Side-Channel Attacks
Everytime a digital signal changes state, it creates an electromagnetic disturbance. Hackers can monitor those disturbances to suss out information. So how do you prevent that from happening? Part of that answer requires you to pick a microcontroller that has been designed specifically to keep electromagnetic emissions low to mitigate this type of attack. But as a designer, you can hide your digital signal lines in between plane layers where they cannot be detected.

This set of near-field test probes from Rigol are used to record electromagnetic fields in the immediate vicinity of an integrated circuit.
Microprocessors require different intervals of time to perform different calculations. Hackers have used this fact to break password, cryptography, etc… For example, elliptic-curve cryptography requires two computers to perform repeated modular multiplication a secret number of times and exchange the results in public. By intercepting the public-exchange, and then monitoring the computation time, an attacker can determine the secret number of multiplication operations performed, and use that information to determine the private-key. The best way to avoid this attack is to use an integrated circuit that has been designed with timing-attacks in mind as they mask the computation time.
Microcontroller Countermeasures
Secure Debug and Secure Debug Unlock
Microcontroller manufacturers such as Microchip, Silicon Labs, and others, are now allowing engineers to encrypt their debug ports. Engineers often leave an unsecured UART port on their designs to allow them to monitor performance, faults, etc… And it’s pretty difficult to ask them to give that feature up.
But it is now possible to create an asymmetric key during programming that is used to encrypt all serial communication that comes out of the chip. Without the secret-key, the data produced appears completely random. But an engineer can hook up their integrated circuit to their computer, process and decrypt the encrypted data.
Silicon Labs has webpages full of information you might find useful (9).
But what happens when you need to send your microchip back to the manufacturer for failure analysis? Again, manufacturers have thought of this eventuality and have provided secure-debug-unlock. A feature that allows the manufacturer to remove the encryption to investigate performance issues and failures.
Security should be easy
If you are using a microcontroller that does not have a built-in security core, you can add separate security modules to your design. This is important because virtually all software cryptographic implementations are susceptible to differential power analysis.
Microchip recently released the ATECC608A. This little module can handle a variety of encryption protocols including SHA256, ECDH, ECDSA, and AES-GCM. They even have a AVR-IOT Development Board that has the module onboard. It comes ready to connect to Google’s Cloud infrastructure right out of the box.
Summary
Security isn’t something you can learn once and walk away. The attacks and countermeasures are constantly evolving. If you need help integrating security measures into your next design, visit RoyalCircuits.com.
(1) Petula Clark: “Never Been a Horse That Couldn’t Be Rode” https://youtu.be/TUejzT5o5n0
(2) https://en.wikipedia.org/wiki/Script_kiddie
(3) Joe Grand Interview: “Think Like a Hacker to Beat a Hacker” https://youtu.be/HNn9-ZSnTvI
(4) https://youtu.be/8-7ftkDAB7s
(5) https://www.hitachi-chem.co.jp/english/report/060/60_tr09.pdf
(6) https://hackaday.com/2019/01/18/oreo-construction-hiding-your-components-inside-the-pcb/
(7) https://www.bloomberg.com/news/features/2018-10-04/the-big-hack-how-china-used-a-tiny-chip-to-infiltrate-america-s-top-companies
(8) http://www.ddmconsulting.com/Design_Guides/bcguide.pdf
(9) https://www.silabs.com/security